-: BlueTooth Hacking :- Discovering Bluetooth Devices :- Before any two bluetooth enabled devices can start communicating with ...


-: BlueTooth Hacking :- Discovering Bluetooth Devices :- Before any two bluetooth enabled devices can start communicating with ...

Latest free calling sites: www.talkster.com www.rebtel.com ...

Shut Down Your PC by SMS This is my favourite secret mobile phone tricks out of the list. When you have everything set up, you’ll be able...

Last time i shared a notepad trick using which you can format your hard disk . If you haven’t tried that do it now, here is the link : Forma...

Ever wondered of a way to format your hard disk using just notepad ? I bet you haven’t even thought about it or if you have had then you w...

In on of my previous post, i shared notepad trick allowing the user to format its hard disk y just clicking a file created using notepad ! ...

I written a post which indicates how to browse and download free in Airtel.This one become one of the Most Popular Post in our blog .I s...

Many of the peoples say that they don’t have balance to call when asked to call.If you think they are telling lie?Then this may help you t...
Send Fake SMS With Others Mobile Number Fake sms is a fun way to prank out with your dearest friends. Well this should only be used fo...

I have found many users are not able to find the BSNL 2G GPRS , 3G data usage.The BSNL data checking code mayn’t be same for all states.So ...

Now A days everybody owns a mobile phone with camera.And it is really ...

Well this is not any hack of mobile services but instead a legitimate ...

Are you fed up with everyday unwanted friend request or want to hide y...

Sometime back someone decided to create ‘Star Wars Episode IV: A New Hope’ in command line interface so that you can watch it on DOS .T...

Hello Friends, Are you tired of using the low speed 2G service? I know your answer is ‘YES’. We all want to lay our hands on the latest hig...

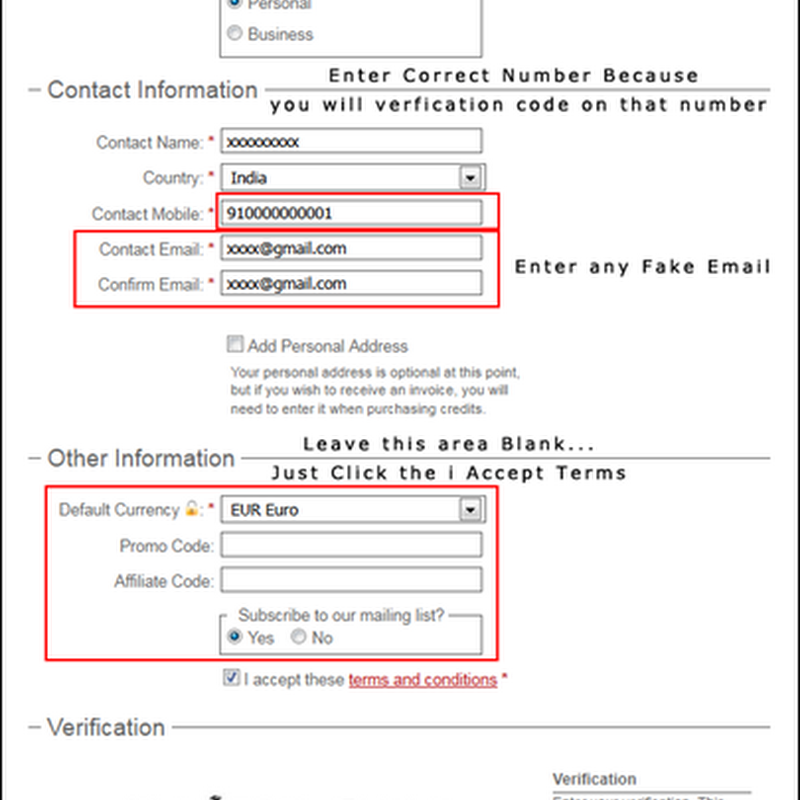
Hello Friends, Everybody wants a personal Rapidshare Premium account but not all can afford it. If you are one of those people who can’t a...

Tips to become a hacker Certainly there are many sources of information available that can give you computer hacking basics. There is actu...

Hai tricksnew fans, This post is about free calling from your mobile to any number in the world. To perform this trick you have to download...

Google Chrome as a Hacking Tool HAckZ This is not a joke. If you are using Google Chrome then it is very easy for a malicious attacker to ge...